Digital Citizen Corner
Free Gift: When Generosity Hides a Trojan Horse
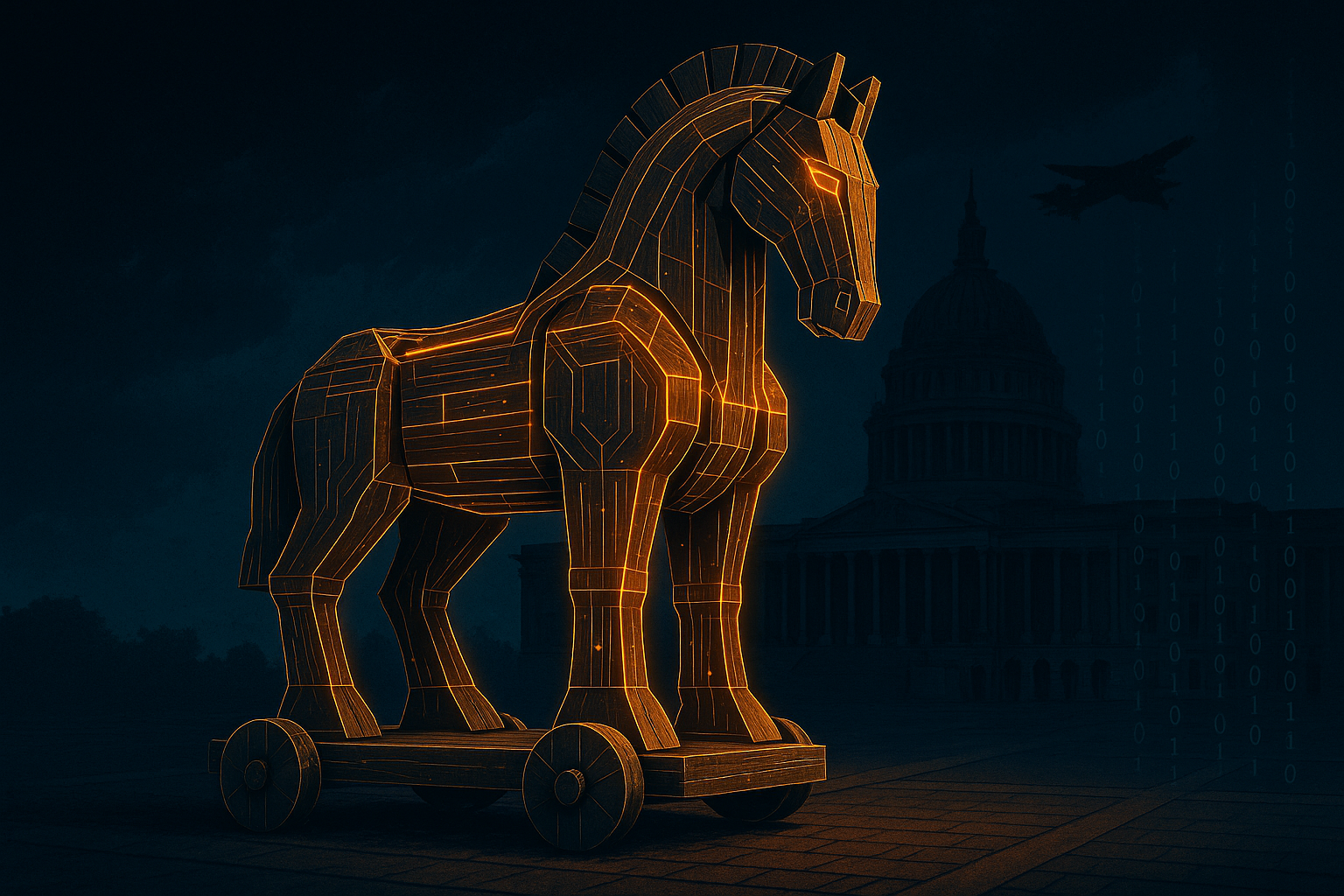
In the world of cybersecurity and digital ethics, few phrases carry as much weight as “free gift.” It sounds generous, harmless—maybe even noble. But sometimes, as history teaches us, the most dangerous things come in the most appealing packages.
The Ancient Trojan Trap
More than 3,000 years ago, the city of Troy stood invincible behind its towering walls. After a decade of failed attempts to breach the city, the Greeks offered what seemed like a peaceful gesture: a large wooden horse, supposedly left behind as a gift before their retreat.
The Trojans—overcome with curiosity and perhaps relief—brought the horse into the city, celebrating what they thought was the end of a long war. But deep inside the wooden statue, Greek soldiers waited in silence. That night, they emerged, opened the gates, and let in their returning army. Troy fell—not through battle, but through deception.
The people of Troy were called Trojans, and to this day, the phrase “Trojan Horse” is used to describe any trick or trap that hides danger inside something appealing.
The Modern Trojan: A $400 Million Jet?
Just a few weeks ago, headlines emerged about President Trump, being set to receive a $400 million Boeing 747-8 aircraft, reportedly as a gift from Qatar. While this move has sparked intense political and diplomatic debate, it also sends a signal to cybersecurity and intelligence communities:
What’s the real cost of a gift that grand? And what if the threat doesn’t sit in the cockpit—but in the code?
In today’s world, a modern Trojan horse doesn’t need to be made of wood. It can come embedded with advanced surveillance systems, backdoor access to communications, or software vulnerabilities that are invisible to the naked eye—but devastating in impact.
It might look like generosity, but hidden inside can be listening devices, spyware, or systems that compromise national security. In the age of cyberwarfare, hardware is no longer neutral.
Why Digital Citizens Should Care
It’s easy to look at international politics and think, “That has nothing to do with me.” But the reality is that everyday digital citizens face their own Trojan Horses all the time:
- Free apps that sell your data.
- Friendly-looking emails with hidden malware.
- Online quizzes that harvest personal info.
- “Limited-time offers” that lead to phishing traps.
In the digital age, “free” often means “you are the product.” Just like the Trojans, we let in danger not through force—but through misplaced trust.
Stay Aware, Stay Secure
So what can we learn from both ancient Troy and today’s headlines?
- Question generosity, especially when it comes from unexpected or powerful sources.
- Read the fine print—whether it’s on a software license, a political gesture, or a so-called “free” digital service.
- Protect your data like you would your home. Use strong passwords, multi-factor authentication, and don’t blindly accept every “update” or “offer.”
- Teach others—especially children, students, and seniors—to spot digital traps and avoid becoming easy targets.
Final Thoughts: Beware the Illusions
The story of Troy wasn’t just about a horse—it was about trust. About the moment we lower our guard and let the wrong thing in.
As digital citizens, we must stay vigilant. A “gift” that seems too good to be true might be just that. Whether it’s a $400 million aircraft or a free app on your phone, ask yourself what might be riding silently inside.
Because in the digital age, the next Trojan horse might not roll through the gates of a city—it might slide quietly into your inbox.
Written by Bryan Senfuma
Bryan is a Digital Rights Advocate, Digital Security Subject Matter Expert, Photographer, and a Writer. His articles aim to simplify complex tech issues and inspire readers to make informed, confident choices online. Email: bryantravolla@gmail.com